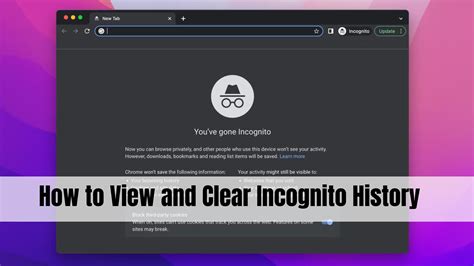
Understanding how to access and view incognito history might seem like a leap into a realm of complex technicalities. However, with the right knowledge and tools, one can navigate this area adeptly. This article delves into the expert perspective on how to uncover incognito history while offering practical insights for users seeking clarity.
Opening Paragraph with Context and Hook
Surfing the web in incognito mode is popular for maintaining privacy. However, there might be instances where one needs to access the incognito history for various reasons, such as parental control or safeguarding one’s own data. Despite the notion that incognito mode ensures anonymity, advanced tools and techniques can reveal browsing history under the guise of privacy. By understanding these methods, users can gain better control over their digital footprints.
Key insights box:
Key Insights
- Primary insight with practical relevance: Tools exist to trace incognito history, albeit not foolproof.
- Technical consideration with clear application: Router logs and third-party software can retrieve incognito data.
- Actionable recommendation: Use network monitoring tools and router logs for better chances of retrieving incognito history.
Key Insights
- Primary insight with practical relevance: Tools exist to trace incognito history, albeit not foolproof.
- Technical consideration with clear application: Router logs and third-party software can retrieve incognito data.
- Actionable recommendation: Use network monitoring tools and router logs for better chances of retrieving incognito history.
Analysis Section 1: Understanding Router Logs
Routers act as the central hub in a network, keeping logs of all connected devices’ activities. These logs, known as the device’s Internet Protocol (IP) address history, can be mined to retrieve browsing information even from incognito sessions. To access these logs, one must have administrative control over the router. These logs are usually available in the router’s admin panel under sections named ‘Logs,’ ‘System Log,’ or ‘Event Log.’ For example, Netgear and Linksys routers typically have straightforward interfaces to access this information.
Analysis Section 2: Leveraging Third-Party Software
Several third-party applications are designed to monitor and retrieve data from incognito sessions. Software like Psiphon, GlassWire, and Firesheep offer capabilities to capture browsing history even when users think they are secure in incognito mode. These applications usually function by monitoring the network traffic and storing it in a log file accessible via the software’s interface. However, the effectiveness of these tools often depends on whether the user’s device is connected directly to the monitored network.
FAQ Section:
Can incognito history be viewed by service providers?
Yes, internet service providers (ISPs) can track the browsing data, including those in incognito mode, since incognito mode does not affect the network level. However, viewing specific URLs visited in incognito mode is generally not possible without additional surveillance techniques.
Is it legal to access incognito history?
The legality of accessing incognito history depends on jurisdiction and context. It’s generally lawful for parents to monitor their children’s browsing or for network administrators to oversee their network’s usage. However, unauthorized access for stalking or other malicious intents is illegal.
Can incognito history be viewed by service providers?
Yes, internet service providers (ISPs) can track the browsing data, including those in incognito mode, since incognito mode does not affect the network level. However, viewing specific URLs visited in incognito mode is generally not possible without additional surveillance techniques.
Is it legal to access incognito history?
The legality of accessing incognito history depends on jurisdiction and context. It’s generally lawful for parents to monitor their children’s browsing or for network administrators to oversee their network’s usage. However, unauthorized access for stalking or other malicious intents is illegal.
This discussion has shed light on the practical methods to access incognito history, backed by technical insights and expert recommendations. Though incognito mode promises privacy, understanding these techniques ensures one can navigate through them effectively. With the proper tools and knowledge, one can retrieve information that initially seems untouchable.